Site Design - 3 - Tactics
3.1 Tactic: Vehicle Bombs
Stationary Vehicle Bombs:
With stationary bombs the aggressor doesnt attempt to crash through
barriers
Attempt to get as close the facility as possible with out risking detection
Historically, the most common type of vehicle bomb attack
Moving Vehicle Bombs:
Aggressor is willing to crash through barriers to reach facility
Perimeter defining standoff must be capable of stopping the threat vehicle
For both cases, standoff distance is the best mitigation
For stationary vehicle bomb:
Boundary is defined such that a vehicle crossing boundary draws attention
and initiates response force action
Maximize distance from parking areas
For moving vehicle bomb:
Boundary must resist the vehicle
Determine design speed based on roadway layout
Minimize direct approaches
Define passive and active barriers
3.2 Tactic: Exterior Attack
This tactic is mainly focused on small improvised explosive devices
The site design can incorporate a exclusive standoff zone to keep
aggressors away from the building and limit their ability to place devices near the building or throw devices towards the building
Clear zone can also be provided around the building so that devices are easier to detect.
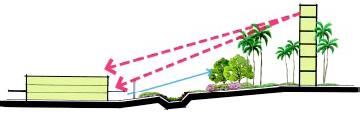
3.3 Tactic: Standoff Weapons
Standoff weapons include mortars, RPGs, and ballistics
Site Design Considerations:
Minimize Vantage Points, locate facility far from vantage points
Consider potential use of predetonation screen (for RPGs) as perimeter
barrier defining standoff if that is applicable tactic
Use of obstruction screens or landscaping to block sightlines

3.4 Tactic: Forced Entry
Tactic involves various levels of tools and explosives to attempt to
breach the security of the facility.
Site Design Considerations:
Clear zone, avoid features that provide concealment for aggressors
Avoid siting the facility near utility passages that may aid aggressor or
secure the utility access points
Focus on security lighting to support IDS
Provide additional fencing or barrier at facility perimeter if necessary
Significant distance between first detection layer and building causes
delay and exposes aggressor to further detection possibilities
3.5 Tactic: Visual Surveillance, Eavesdropping
Similar to standoff weapons, you want to eliminate or control vantage
points including nearby buildings
Provide clear zone adjacent to buildings so aggressors cant hide near
the building
Consider using perimeter barrier to provide concealment and obscure
assets
To receive your Physical Vulnerability Assessment, please submit your payment of $999.00
B E T T E R: Please submit your payment of $1999.00 for a complete Physical Vulnerability Assessment or Design covering a single location.
| 

